
CYBER SECURITY | 6 MIN READ
In some ways, maintaining the network security of a regular office can be easier than managing a remote office. As a Managed Service Provider, we aim to use our cyber security expertise to educate our audience about how to build and secure a remote office. Keep reading for a few quick remote work cyber security tips.
Here's our top five cyber security tips for remote workers:
-
Install a VPN
-
Know How to Spot a Phishing Attack
-
Create a BCDR Plan
-
Set Up Secure File-Sharing
-
Institute a Company-Wide Protocol
For more information on each tip, keep reading!
Install a VPN
VPN's, also known as Virtual Private Networks, are a software that can be used in conjunction with public or home WiFi to ensure that data is encrypted when being sent along a public Internet signal to and from your office's network.
VPN's authenticate your information with your network's firewall before allowing it through, which ensures that information is encrypted and your network is still secure when all employees are sending information, logging into programs, and communicating with each other.
Even if employees aren't handling sensitive data, it is a good rule of thumb to ask everyone to always sign into a VPN before going to work online remotely.
Make sure that every employee has a VPN installed and set up on their computers before taking your office remote. Your network should already have a corporate VPN, so you can set your office up on that and make sure that everyone is trained on how to use it.
Configuring VPN's for all employees is arguably the most crucial step in setting up your office to go remote because it ensures that your network is still secure even when everyone is out of the office.
Without a VPN, hackers could access sensitive information that employees are sending to each other over public WiFi.
Know How to Spot a Phishing Attack
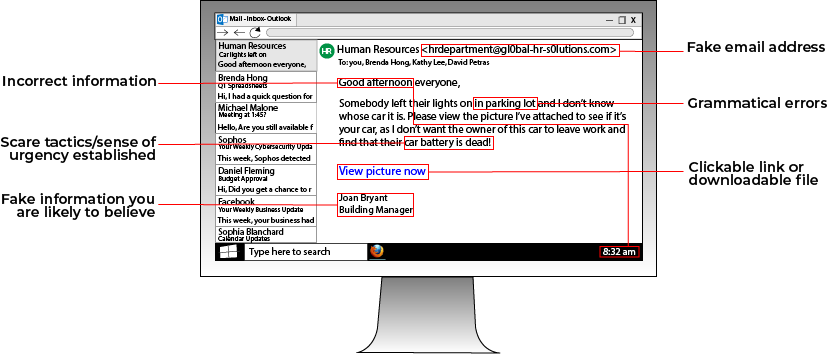
Since workers in a remote office cannot meet face-to-face, email becomes the king of communication. Hackers know this, which is why they can use phishing attacks to hack your network.
While computers are designed to not make mistakes, hackers know that humans are prone to errors. That is why they exploit human error to gain access to a network and deploy ransomware. A popular way that hackers gain access to a network is through phishing attacks.
Phishing attacks involve a hacker sending an email containing a malware-loaded link to a potential victim. The email can either contain an enticing offer, such as "Click this link for a free cruise!' or can be faked to resemble a legitimate company. For instance, a hacker posing as Google could email a victim telling them to click a link to update their email storage.
Always be wary of emails from people you don't know telling you to click a link. If you want to see if an email is a phishing email, you can look at the address that the email is from. For instance, a phishing email posing as Facebook that has the email address "security@fakebookalerts.live" is probably a fake address.
Make sure that the address is spelled correctly too with no character substitutions. While an address from "@facebook.com" might be legitimate, an email from "@facebo0k.com" is probably a phishing attempt.
Another way to test a phishing email is to try and find the page the email is referencing without clicking the link. For instance, if the email is from Microsoft and is telling you to update your storage, try doing that through the official Microsoft website instead of through the link. If you can't find such a page, then the email is most likely a phishing attempt.
In general, most legitimate emails don't ask you to click a link to validate or update information, so your internal warning signals should flash as soon as you see this. If you feel suspicious about an email, try calling the company who it's from to ask about the email, along with other verification methods.
Create a BCDR Plan

If your company doesn't have a BCDR (Business Continuity Disaster Recovery) plan, consider setting up at least the foundations of one before taking your office remote.
Network outages and ransomware attacks can happen even when your office is remote, so ensure that your business can avoid lengthy downtime by taking a few simple steps.
Make sure that your business' data is automatically backed up as often as possible. In the event of a network outage or ransomware attack, you may have to restore all devices to the most recent backup. If you don't back up data frequently, you risk losing access to important documents.
Additionally, make sure that all executives and any in-house IT staff know the proper steps to take in the event that your network is breached or stops working. This will minimize downtime and ensure that everybody is on the same page.
RELATED: What Is Phishing? [Types and Tips to Prevent]
Set Up Secure File-Sharing
Remote working doesn't halt the sharing of private documents and sensitive information. Setting up secure file-sharing platforms ensures that business continues to flow smoothly and securely.
Platforms such as OneDrive or ShareSync let you open and view your synced files directly from your phone and share files with co-workers and clients.
Keep in mind that if you have a Managed Service Provider, you may already have a secure file-sharing service bundled into your cyber security package, which will save you the cost of having to buy one of these platforms.
Business phones may also come with a feature called “Find Me Follow Me”, or twinning. With this feature, calls are forwarded from an employee's desk phone to their mobile phone.
If that employee doesn’t pick up after a few rings, instead of letting someone leave a voicemail on their mobile phone, which can mean that sensitive information is now stored on an employee's personal device, the call is re-routed back to that employee's desk phone so someone can leave a voicemail there instead.
Then, a transcript of the voicemail is emailed to that employee. This feature lets you control where your company's data is stored by ensuring that no voicemails that may contain sensitive data are left on an employee's personal device. If you have this feature, enable it before taking your office remote.
Institute a Company-Wide Protocol
While having a VPN and a password policy are great ways to protect your network while working remotely, sometimes the greatest potential network threat is a lack of open communication among your staff.
If an issue or threat pops up in your network, make sure that your staff understands the proper channels for communicating issues. In the event of a network breach or outage, your staff should know the emergency action plan that will be put into effect.
If you want to ensure that all staff are up-to-speed on cyber security do's and do not's, start by laying out a policy with a few basic tenants.
A main aspect of a cyber security policy should be the rules surrounding file-sharing. Especially if your company has to comply with data regulations such as HIPAA, you need to ensure that staff know how to share files with one another securely without putting your company's private data at risk.
Once you implement the points from the previous section, make sure that staff are trained on how to use the file-sharing software and can set up the "Find Me Follow Me" feature on their business phones.
While file-sharing procedures is a great first tenant to include in a cyber security protocol, instituting a password policy is another step you can take to ensure that data is safe and accounts aren't at risk of becoming breached.
Password policies educate your employees on how to create and maintain secure passwords. Basic aspects of a password policy could include points about making passphrases instead of passwords, not writing down passwords anywhere, and enabling two-factor authentication whenever possible.
When working remotely, securing your network is crucial. Consider working with a managed services provider who can protect your network for you, removing the stress and cost of doing it yourself.
A managed services provider, also known as an MSP, can assist you in setting up and maintaining a remote environment. They can act as a help desk for employees experiencing network issues to call into for assistance.
Cyber threats are constantly evolving. Stay ahead of them by upgrading your cyber security today.
Posted by Erica Kastner

Erica Kastner is a lead Marketing Specialist at Standard Office Systems as well as a University of Georgia graduate. She aims to use her passion for problem-solving to help businesses understand how to better leverage their network infrastructure.

